Predicate Vault
Available for Pro / Teams / Enterprise
Predicate Vault is available exclusively for Pro, Teams, and Enterprise tier users. The open-source sidecar and SDKs remain free for local development and single-agent deployments. Open Vault →
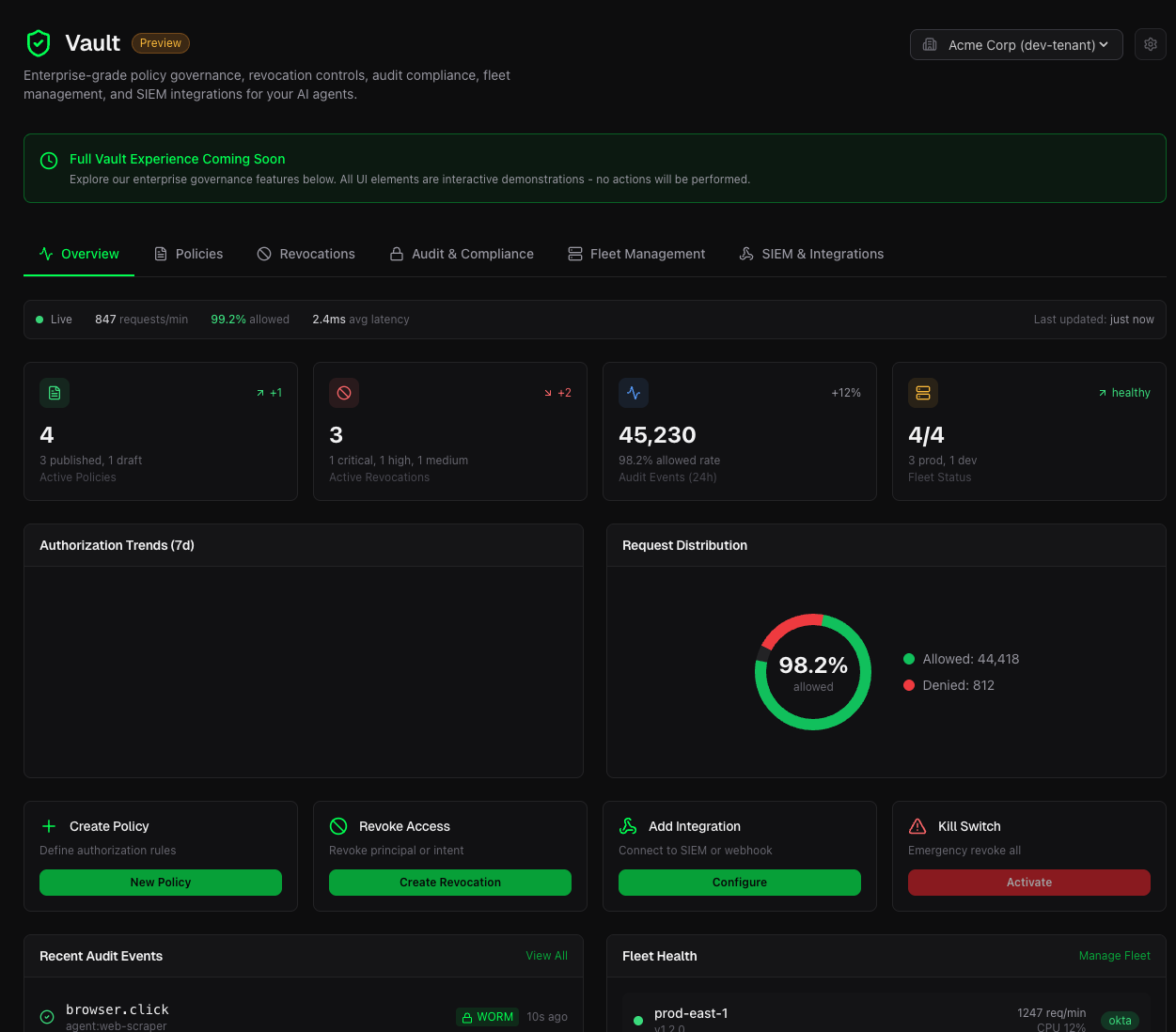
Predicate Vault is the Control Plane and Audit system for managing AI agent authorization at scale.
If the IdP token is the passport, and the Sidecar is the border guard checking the visa — Vault is the Embassy. It's where visas are issued, revoked, and audited.
What is Predicate Vault?
While the sidecar acts as the local enforcer (the border guard), Vault is your command center (the embassy). It extends the Predicate Authority sidecar with centralized management capabilities that security teams need when operating fleets of AI agents in regulated environments.
Vault transforms scattered sidecars into a unified, auditable fleet:
- Manage policies centrally and push updates to all sidecars instantly
- Revoke compromised agents or intent hashes with global kill-switches
- Audit every authorization decision with WORM-ready, tamper-evident logging
- Monitor your entire fleet of sidecars in real-time
- Integrate with existing SIEM and security infrastructure
How It Differs From What You Have Today
Developers immediately pattern-match new tools against things they already know. Let's address that upfront.
Why not just use local SQLite and Datadog?
| What You Have | The Problem | What Vault Provides |
|---|---|---|
| Local SQLite | Logs scattered across machines. Manual collection for audits. No tamper evidence. | Unified, Merkle-anchored audit. One-click compliance exports. |
| YAML policy files | Version drift. SSH into each machine. No rollback. No visibility. | Single source of truth. Push-button deployment. Git-like history. |
| Prometheus + Grafana | Shows latency and request counts, but no decision context or policy correlation. | Every decision with full context. Policy rule attribution. |
Core Capabilities
Centralized Policy Management (The End of YAML Drift)
Managing YAML files across dozens of sidecars leads to version drift and manual SSH updates. Vault provides a single source of truth with push-button deployment, full revision history, and instant rollback.
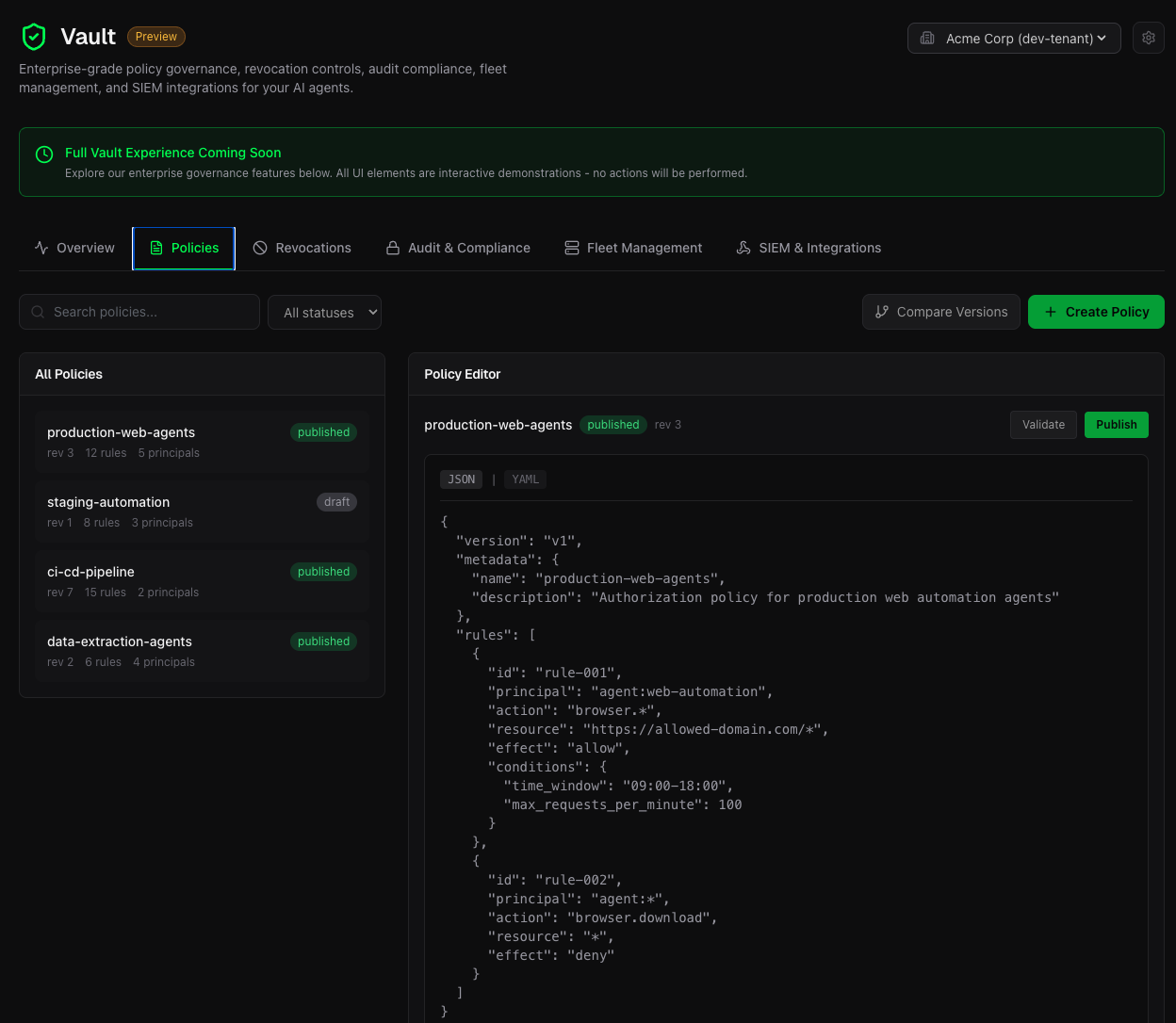
- Editor: JSON/YAML with syntax highlighting and validation
- History: Every revision saved with diff view
- Deployment: Push to all sidecars or target specific groups
- Rollback: One-click revert to any previous version
Global Kill-Switches (Stop a Compromised Agent in Milliseconds)
When an agent is compromised, you need to stop it immediately. Vault's kill-switches revoke by principal or intent hash, syncing to all sidecars in milliseconds.
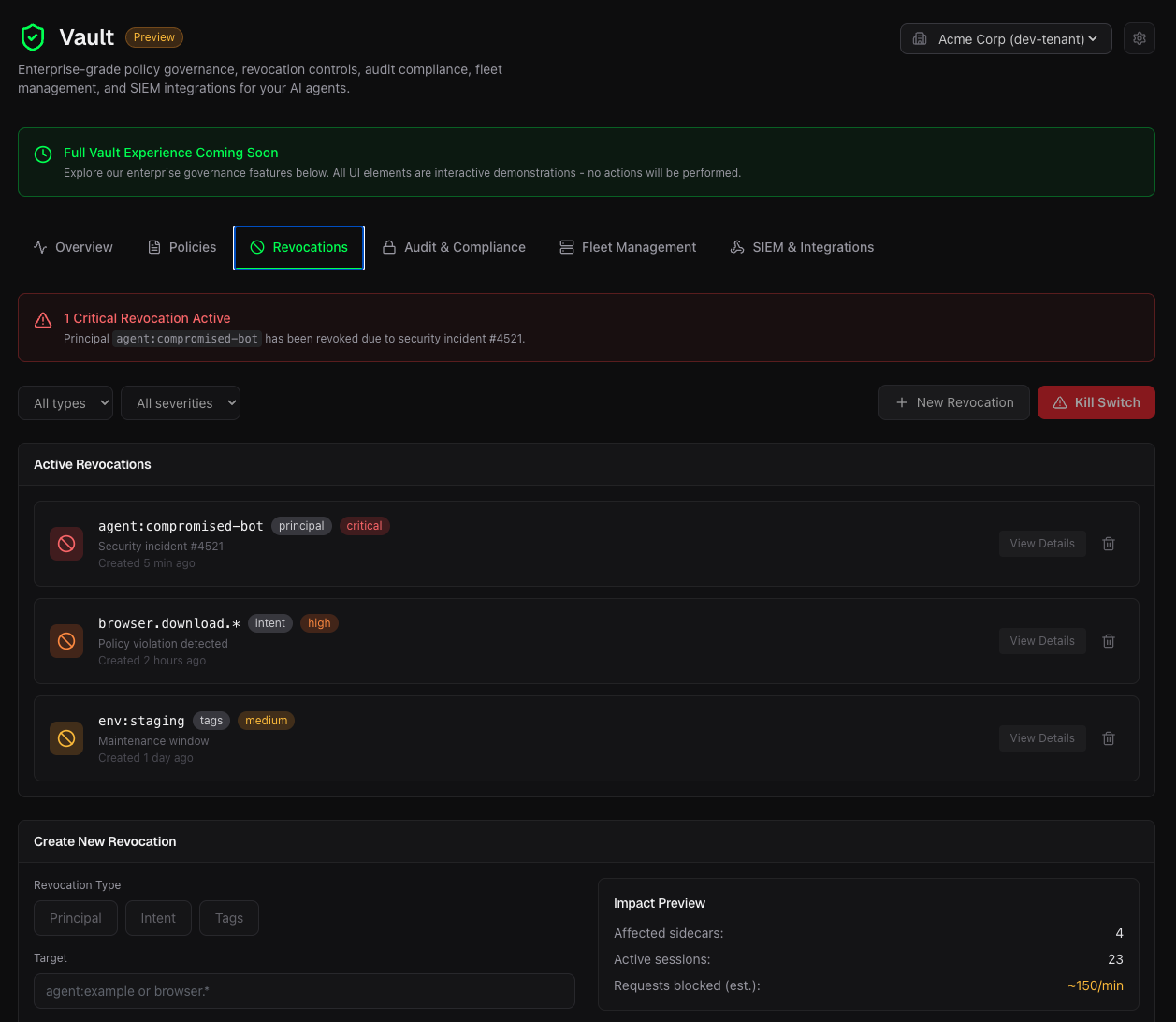
- Principal revocation: Block a specific agent identity across all sidecars
- Intent hash revocation: Block a specific action pattern everywhere
- Kill switch: Emergency button to deny all requests
- Expiration: Time-limited revocations with auto-expire
WORM-Ready Audit Logging (Prove What Your Agents Did)
Compliance requirements demand immutable, verifiable audit trails. Every event is Merkle-tree anchored for tamper evidence, with 7-year WORM retention for SOC2, HIPAA, and regulatory audits.
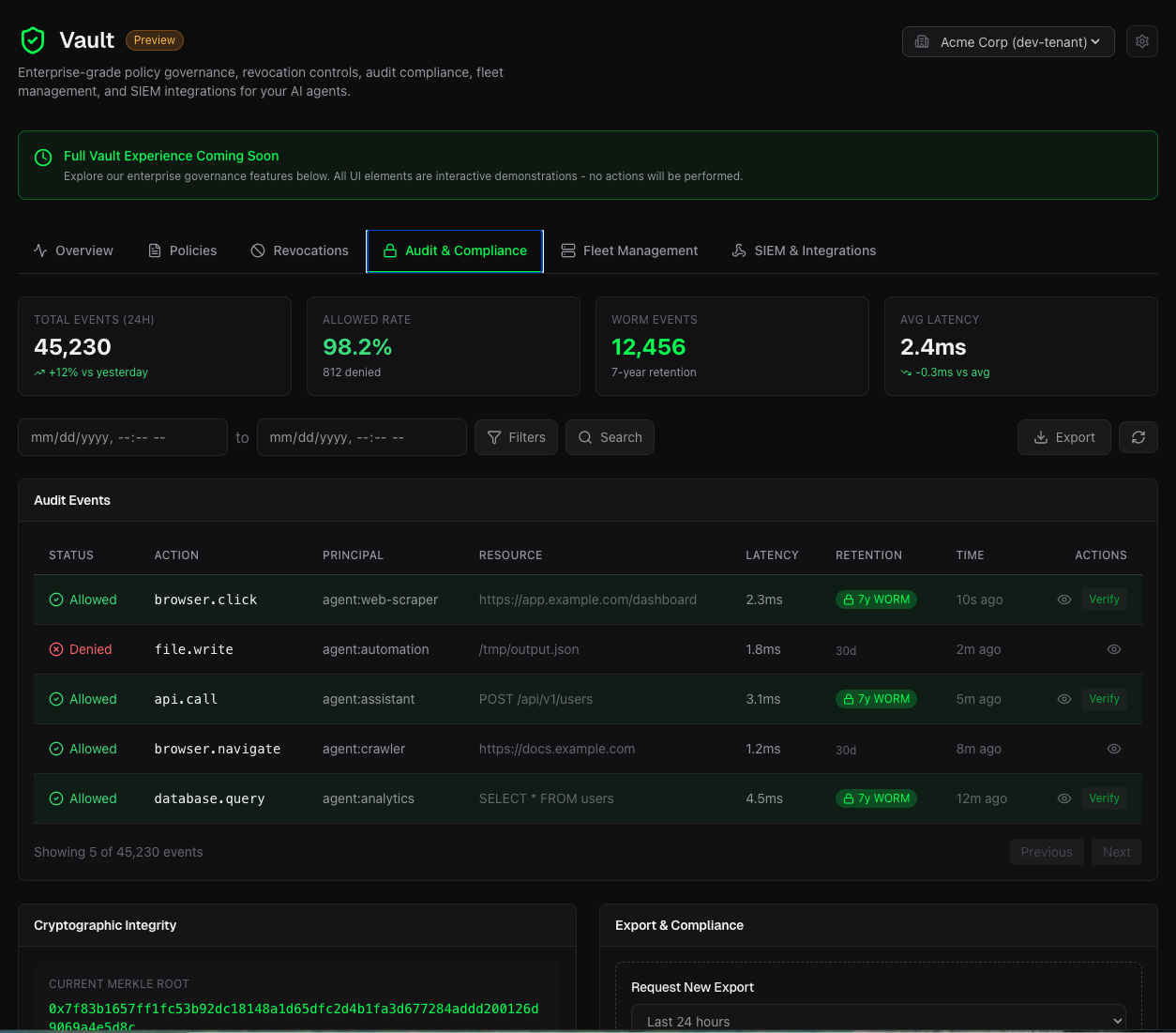
- WORM events: Immutable, cryptographically signed
- Full context: Captures principal, action, resource, decision, and mandate
- Search & Filter: By principal, action, resource, decision, time range
- Export: CSV, JSON for compliance reports
- Verify: Merkle proof verification for any event
Fleet Management (Hundreds of Sidecars, One Dashboard)
Manage your entire fleet from a single dashboard. Real-time health, resource monitoring, and support for enterprise identity providers.
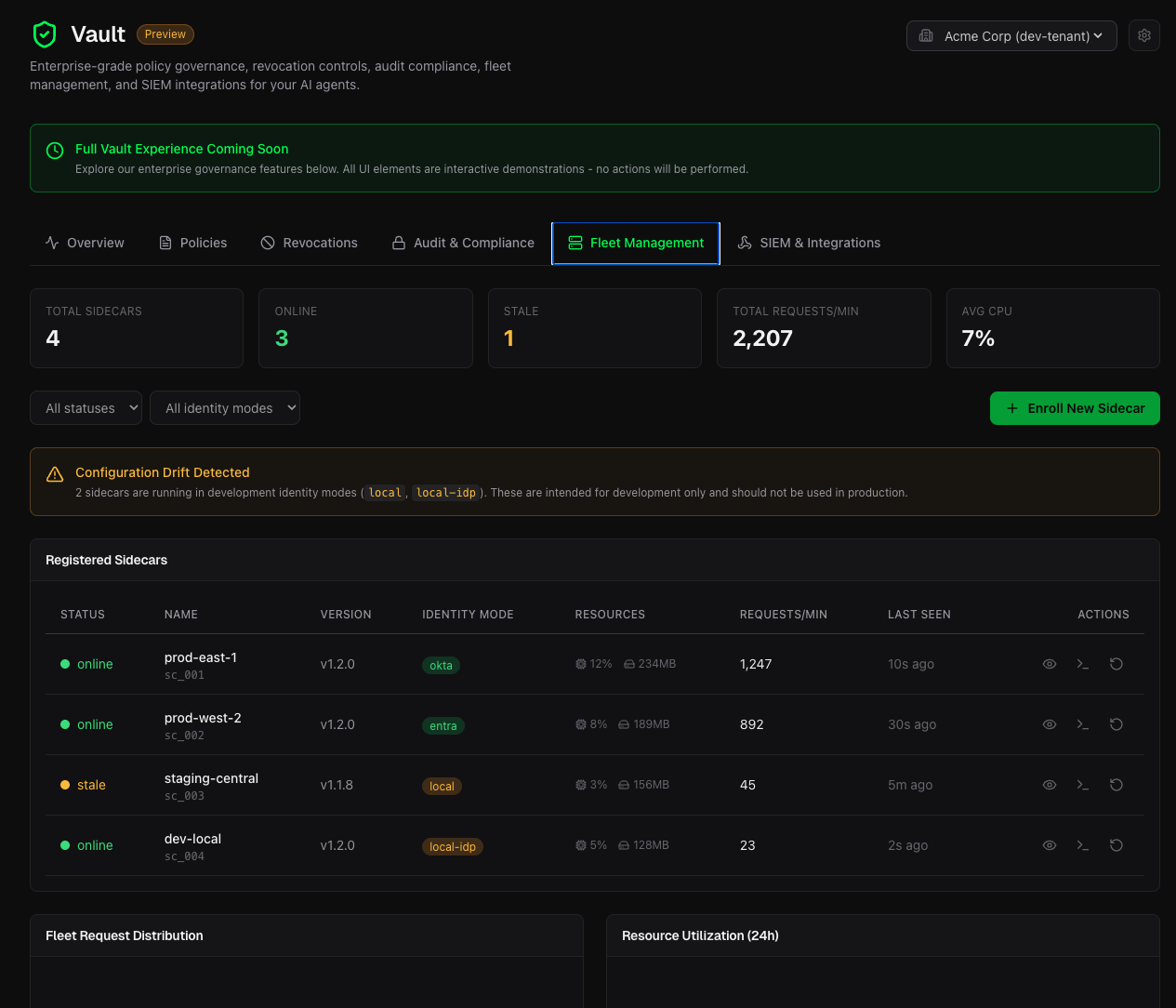
- Real-time status: See which sidecars are healthy, degraded, or offline
- Resource monitoring: Track CPU, memory, and authorization latency
- Identity modes: Okta, Entra ID, OIDC, and local identity providers
- Enrollment: Secure registration tokens for easy sidecar enrollment
SIEM Integrations (Stream to Your Security Stack)
Stream authorization events to your existing security infrastructure with pre-built connectors and custom webhook support.
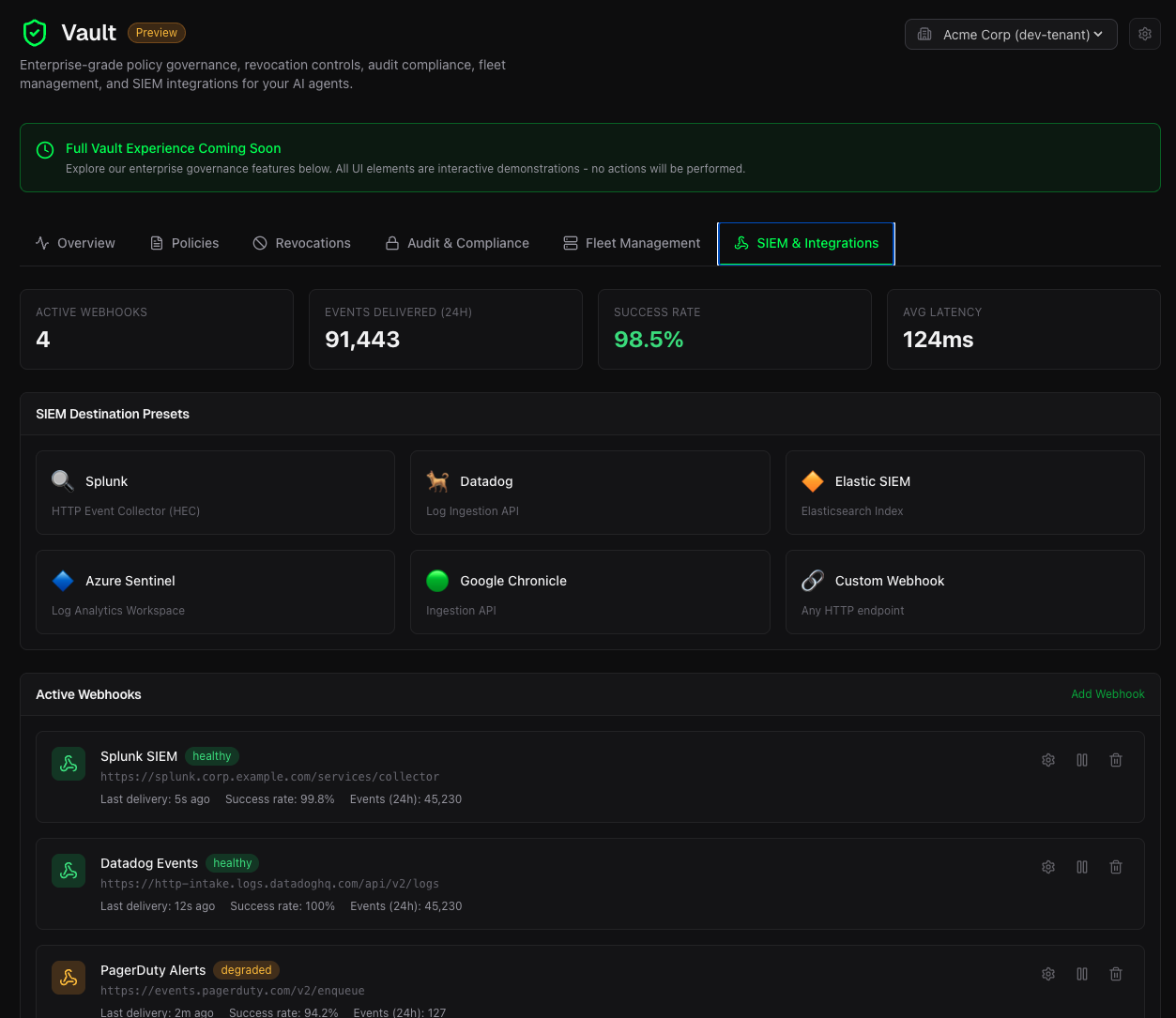
- Pre-built connectors: Splunk, Datadog, Microsoft Sentinel
- Webhook support: Custom integrations via configurable webhooks
- Event filtering: Send only the events you care about
- Real-time streaming: Sub-second event delivery
Architecture
┌─────────────────────────────────────────────────────────────────┐
│ Predicate Vault │
│ ┌─────────────┐ ┌─────────────┐ ┌─────────────┐ │
│ │ Policies │ │ Revocations │ │ Audit │ │
│ │ Manager │ │ Manager │ │ Vault │ │
│ └──────┬──────┘ └──────┬──────┘ └──────┬──────┘ │
│ │ │ │ │
│ └────────────────┼────────────────┘ │
│ │ │
│ ┌──────▼──────┐ │
│ │ Fleet Sync │ │
│ │ Engine │ │
│ └──────┬──────┘ │
└──────────────────────────┼───────────────────────────────────────┘
│
┌───────────────┼───────────────┐
│ │ │
┌─────▼─────┐ ┌─────▼─────┐ ┌─────▼─────┐
│ Sidecar │ │ Sidecar │ │ Sidecar │
│ Agent 1 │ │ Agent 2 │ │ Agent N │
└───────────┘ └───────────┘ └───────────┘Future Roadmap
We're building more than a control plane. Here's what's coming:
Blast-Radius Simulation
Before deploying a strict new policy to your fleet, Vault will simulate the policy against your last 30 days of audit logs to show you exactly how many legitimate agent actions would have been blocked. Enterprise teams love this—it reduces the fear of breaking production.
Deterministic Post-Execution Verification
Pre-execution auth stops the attack. Soon, Vault will store cryptographic state-diff proofs (e.g., filesystem changes, DOM snapshots) to prove an agent actually succeeded at the authorized task. Not just "did it try?"—but "did it work?"
LLM-Assisted Policy Drafting
Draft strict, YAML-based Predicate policies using natural language (e.g., "Allow the agent to read S3 but block all internet egress"), which Vault compiles into deterministic rules. Human-readable intent, machine-enforceable policy.
Getting Started
Pro, Teams, and Enterprise users can access Vault directly from the dashboard:
Open Predicate Vault →
For local development, use the open-source sidecar and SDKs: